Kids Data Privacy Statistics 2024
Is your child the creator or the product being harvested? We’re allowing apps to track our children’s every tap and swipe, turning their development into a data point for corporations. It is time to reclaim the screen as a tool for personal sovereignty and creative mastery instead of a nuisance of surveillance.
Modern parenting requires a shift in perspective. We often view technology as a digital babysitter or a necessary distraction. However, when a device is configured only for consumption, it becomes a liability. Your child’s digital footprint begins before they can even speak, fueled by “sharenting” and aggressive data harvesting from free-to-play games.
Transforming technology from a nuisance into an asset starts with understanding the hidden machinery of the internet. We must move away from a “set it and forget it” mentality. True digital sovereignty means teaching kids to build, create, and protect their identity in an era of total transparency.
Kids Data Privacy Statistics 2024
The scale of data collection targeting minors has reached unprecedented levels. Modern ad tech is designed to profile users with surgical precision. For children, this profiling happens during critical developmental windows, creating a permanent digital record that they did not consent to.
Recent data shows that by the time a child turns 14, an estimated 76 million data points have been collected about them. These data points include everything from location history and search queries to biometric markers and behavioral patterns. This digital dossier follows them into adulthood, potentially affecting future opportunities.
Breaches are also becoming more frequent and severe. In 2022 alone, 1.7 million children fell victim to data breaches, meaning 1 in 43 kids had their personal information compromised. The PowerSchool breach in late 2024 further highlighted this vulnerability, affecting 62 million students globally and exposing sensitive academic and family records.
Regulatory bodies are struggling to keep pace, but fines are increasing. The Federal Trade Commission (FTC) recently settled with Disney for $10 million and the developer of Genshin Impact for $20 million over COPPA violations. Despite these actions, nearly 99% of websites and apps aimed at children still use deceptive “dark patterns” to manipulate users for commercial gain.
The urgency of this issue is reflected in public sentiment. Around 89% of Americans report significant concern regarding how social media platforms gather information on minors. With 96% of U.S. teens using the internet daily, and 46% reporting they are online “almost constantly,” the window for intervention is closing.
How the Digital Harvesting Machine Works
Data harvesting is not a single event but a continuous process of extraction. It begins with the Software Development Kits (SDKs) embedded in popular apps. These invisible packages of code allow third-party advertisers to “piggyback” on an app’s permissions to collect device IDs and location data.
Behavioral profiling uses these data points to build a predictive model of your child. Algorithms track how long a child hovers over an image, which colors they click on most frequently, and their emotional response to specific triggers. This information is then sold on real-time bidding (RTB) exchanges to the highest bidder.
Cross-device tracking ensures that the harvesting doesn’t stop when the tablet is turned off. If your child uses a laptop for school and a console for gaming, companies link these identities using shared Wi-Fi networks and login credentials. This creates a 360-degree view of their daily life, habits, and social circles.
Deceptive design, or “dark patterns,” plays a massive role in this system. Apps often use bright colors, “streaks,” and variable reward schedules to keep children engaged for as long as possible. The longer the engagement, the more data is generated. These tactics exploit the underdeveloped impulse control of the adolescent brain.
Benefits of Reclaiming the Screen
Shifting from a surveillance-heavy digital diet to a privacy-focused one offers measurable developmental advantages. When children are not being constantly nudged by algorithms, they regain the ability to focus. This fosters deep work habits that are essential for high-level creative mastery.
Personal sovereignty is the primary benefit of this approach. By limiting data exposure, you protect your child’s future “self” from the consequences of a permanent digital record. They are free to experiment, make mistakes, and evolve without those actions being weaponized by a credit scoring algorithm or a future employer.
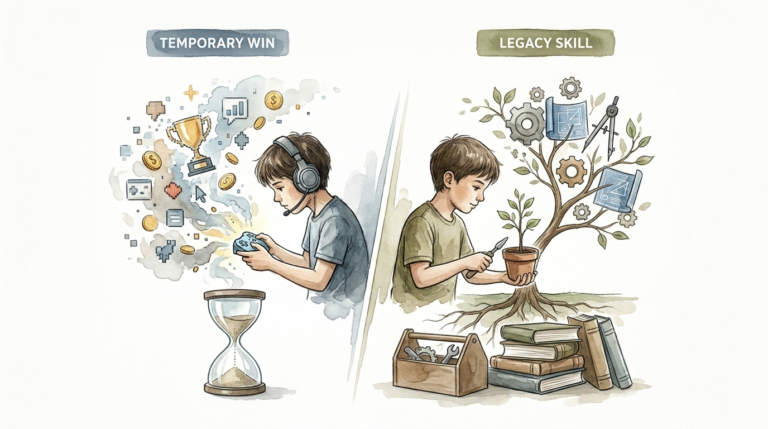
Creative mastery becomes the focus when consumption is curtailed. Instead of scrolling through an endless feed of “nuisance” content, children can use devices as “assets” for coding, digital art, music production, or 3D modeling. This turns the screen into a workshop rather than a Skinner box.
Cognitive resilience is another long-term gain. Children who understand how they are being tracked become savvy digital citizens. They learn to spot manipulation and value their own attention as a finite resource. This skepticism is a vital survival skill in an AI-driven economy.
Challenges and Common Pitfalls
Parents often fall into the trap of “Free App Fallacy.” If an app is free, the child is the product. Many “educational” apps are actually data-gathering engines in disguise. Avoiding these requires a shift toward paid, privacy-respecting alternatives that do not rely on ad revenue.
Hand-me-down devices represent a major security loophole. When you give a child an old phone, it often retains your accounts, tracking cookies, and advertising profiles. This “pollutes” the child’s data profile with your habits while exposing them to adult-targeted content and trackers.
School-issued technology is another hurdle. Many educational institutions mandate the use of platforms that have questionable privacy track records. Parents often feel they have no choice but to comply, creating a situation where the “nuisance” tech is forced into the home by a trusted authority.
The “Sharenting” phenomenon is a pitfall that begins at home. Every photo posted to social media contributes to a child’s digital footprint. Facial recognition algorithms can now link a toddler’s photo to their adult profile with high accuracy, effectively removing their “right to be forgotten” before they even turn ten.
Limitations of Current Privacy Tools
Privacy is not a binary state but a spectrum of risk. Even the best parental controls have limitations. Many hardware-based solutions can be bypassed by a determined teenager with a basic understanding of VPNs or MAC address spoofing.
Technological boundaries are often at odds with social integration. If every other child in a peer group is on a specific platform, a child who is restricted from it may face social isolation. This trade-off between privacy and belonging is one of the hardest challenges for modern families to navigate.
Encryption is a powerful tool, but it is not a silver bullet. While end-to-end encryption protects the content of messages, metadata—who your child talks to, when, and for how long—is still visible to many service providers. This metadata is often just as valuable to profilers as the messages themselves.
State-level legislation is fragmented and inconsistent. While California and Connecticut have introduced robust children’s privacy laws, many other regions have no protections at all. Relying on the law to protect your child’s data is a reactive strategy that often fails against global tech giants.
Nuisance Tech vs. Asset Tech
Understanding the difference between technology that drains a child’s potential and technology that builds it is crucial. The following table compares the two approaches across key metrics.
| Feature | Nuisance Tech (The Product) | Asset Tech (The Creator) |
|---|---|---|
| Primary Goal | Maximizing engagement and data points. | Facilitating skill acquisition and creation. |
| Revenue Model | Ad-supported or “Free-to-Play.” | Direct purchase or open source. |
| User Experience | Passive consumption (infinite scroll). | Active participation (IDEs, DAW, CAD). |
| Privacy Level | Extensive tracking and profiling. | Local storage and data minimization. |
| Impact on Brain | Dopamine loops and short attention. | Flow states and deep problem solving. |
Practical Tips for Digital Sovereignty
Securing your home network is the first line of defense. Use a DNS-based filtering service to block trackers at the router level. This prevents smart TVs, consoles, and tablets from communicating with known data-harvesting domains before the data even leaves your house.
Device-specific settings should be audited monthly. Disable “Personalized Ads” and “Location History” on all family accounts. On iOS, utilize the “App Tracking Transparency” feature to deny tracking requests. On Android, leverage the “Privacy Dashboard” to see which apps are accessing the microphone or camera.
Hardware choices matter deeply. Consider “dumb” devices for younger children or dedicated creative tablets like the Remarkable or an iPad strictly configured with “Screen Time” restrictions. Avoid IoT “smart toys” that have microphones and Wi-Fi connectivity, as these are notoriously insecure.
Teaching “Digital Hygiene” is more effective than simple bans. Explain to your children that their “attention is money” for tech companies. Encourage them to use aliases, avoid linking social accounts, and use search engines like DuckDuckGo or Brave Search that don’t build user profiles.
Advanced Considerations for Practitioners
Serious practitioners may want to move beyond consumer-grade solutions. Setting up a “Pi-hole” on a Raspberry Pi allows for network-wide ad blocking and detailed monitoring of outbound traffic. This provides a granular look at which apps are attempting to “phone home” with user data.
Self-hosting services is the ultimate way to reclaim the screen. Instead of using Google Photos or iCloud, you can host a Nextcloud instance on a home server. This keeps all family photos, documents, and calendars within your physical control, entirely bypassing the cloud-harvesting infrastructure.
Decentralized identities and “Web3” concepts offer a glimpse into the future of privacy. While still experimental, these technologies aim to give users control over their own “attestations” rather than relying on centralized platforms. Understanding these concepts helps prepare children for a world where data is owned by the individual.
Open-source operating systems like GrapheneOS or LineageOS provide much higher privacy floors than standard Android. For older children who are tech-savvy, using these systems can be a powerful lesson in computing. It teaches them that they do not have to accept the “surveillance defaults” provided by major manufacturers.
Scenario: The Protected Child vs. The Harvested Child
Imagine two children, Leo and Sam, both age 10. Leo uses “Nuisance Tech.” He plays free mobile games that track his location every five minutes. The game’s SDK shares his device ID with 40 different ad networks. By lunchtime, ad tech firms know his favorite colors, his approximate home address, and that he is susceptible to “fear of missing out” (FOMO) triggers.
Sam uses “Asset Tech.” His tablet is an older model with no SIM card, running only a few paid apps for drawing and stop-motion animation. His home network uses a DNS filter that blocks 95% of background telemetry. Sam spends his afternoon learning how to layer frames in his animation app. No data points are generated, and his digital footprint remains non-existent.
Ten years later, Leo’s data profile is massive. It contains every impulse he’s ever had, every search he’s ever made, and a history of his location. Sam’s digital profile is a blank slate, but his portfolio is full of creative work. Sam enters adulthood with full personal sovereignty, while Leo is a “harvested product” whose future is already mapped by algorithms.
Final Thoughts
Reclaiming the screen is not about living in the past or fearing the future. It is about ensuring that technology serves the human, rather than the human serving the machine. When we treat a child’s data as a sacred asset, we protect their ability to become autonomous, creative adults.
Surveillance is a nuisance that we have normalized for the sake of convenience. By shifting our focus toward privacy-first tools and creative mastery, we turn devices into powerful assets for growth. Every step toward digital sovereignty is a victory for your child’s future.
Start small by auditing one device today. Replace one “free” ad-supported game with a creative tool that works offline. The transition from product to creator doesn’t happen overnight, but the long-term rewards for your child’s mental health and personal freedom are immeasurable.
Sources
1 videoweek.com (https://videoweek.com/2017/12/14/ad-tech-collects-72-million-data-points-on-the-average-american-child-by-age-13/) | 2 accesspartnership.com (https://accesspartnership.com/opinion/2024-data-reveals-the-urgent-need-for-a-village-approach-to-child-online-safety/) | 3 alanstevens.com.au (https://alanstevens.com.au/blogs/the-76-million-data-points/) | 4 staysafeonline.org (https://www.staysafeonline.org/articles/protecting-our-kids-data-privacy-is-paramount) | 5 blindinsight.com (https://www.blindinsight.com/insights/why-school-districts-are-racing-to-adopt-privacy-preserving-technologies-a-response-to-rising-data-protection-demands) | 6 enzuzo.com (https://www.enzuzo.com/blog/data-privacy-statistics) | 7 ico.org.uk (https://ico.org.uk/media2/about-the-ico/documents/4031562/children-s-data-lives-report.pdf) | 8 koombea.com (https://www.koombea.com/blog/edtech-privacy/) | 9 explorelearning.com (https://frax.explorelearning.com/resources/insights/edtech-data-security-challenges) | 10 huschblackwell.com (https://www.huschblackwell.com/2024-state-childrens-privacy-law-tracker) | 11 cam.ac.uk (https://www.jbs.cam.ac.uk/2024/how-digital-media-impacts-child-development/) | 12 5rightsfoundation.com (https://5rightsfoundation.com/children-face-greater-privacy-risks-today-than-a-decade-ago-and-tech-companies-are-to-blame/) | 13 researchgate.net (https://www.researchgate.net/publication/385304295_Digital_Location_Tracking_of_Children_and_Adolescents_A_Theoretical_Framework_and_Review) | 14 medium.com (https://medium.com/journal-of-engaged-research/from-night-flying-to-visible-horizons-examining-the-relationship-between-immersive-technology-and-4be008689256) | 15 gibsondunn.com (https://www.gibsondunn.com/ftc-updates-to-coppa-rule-impose-new-compliance-obligations-for-online-services-that-collect-data-from-children/) | 16 marketintelo.com (https://marketintelo.com/report/data-privacy-in-education-market) | 17 nih.gov (https://pmc.ncbi.nlm.nih.gov/articles/PMC11843666/)